Transatel wins IoT Global Awards 2024
20/02/2024
UK MVNO Abzorb unifies business communications with Transatel
19/02/2024
Transatel shortlisted for the IoT Global Awards 2024
31/01/2024
Transatel and O2 Telefónica cooperates to launch an ecosystem-play for IoT applications
30/10/2023
With Transatel, Ecotalk leads the Green Revolution in the Cotswolds, UK
25/10/2023
NTT – Transatel earns recognition as a Major Player in IDC MarketScape: Worldwide Managed IoT Connectivity Services 2023 Vendor Assessment
11/10/2023
Ubigi wins MVNO of the Year Awards 2023 in the Consumers’ Champion category
10/10/2023
With Transatel, Groupe Convergence leverages mobile to accelerate digital transformation
28/09/2023
Transatel redefines cellular IoT connectivity boundaries by signing 3 strategic partnerships with satellite network operators Stellar, Skylo and Sateliot.
27/09/2023
Transatel chosen by Toulouse Métropole to ensure continuity between its private Hi5 5G network and public cellular networks for emergency services during the Rugby World Cup.
07/09/2023
Meet Transatel at Hardware Pioneers Max 2023!
26/06/2023
Meet Transatel at Connected North Manchester 2023!
04/04/2023
Meet Transatel at Autonomy Mobility World Expo 2023!
16/03/2023
Transatel NTT joins EUWENA with the promise of building a bridge for service continuity between private and public cellular networks globally.
28/02/2023
Rencontrez nos équipes à IT Partners 2023!
20/02/2023
Meet us at the Mobile World Congress 2023!
15/01/2023
Ubigi cellular data connectivity is now included in the new BMW 7 Series in Japan.
22/11/2022
Ubigi eSIM service joins NTT Resonant’s loyalty program
14/11/2022
Join Transatel at the upcoming IoT Tech Expo Global in London
07/11/2022
NTT, awarded the Leading Champion Private LTE/5G Network Vendor by Kaleido Intelligence
14/10/2022
Transatel and Capestone simplified the deployment of managed cellular solutions
03/10/2022
Why the end of the physical SIM card is great news for enterprises and travelers
30/09/2022
NTT Transatel, recognized as a High Flyer in the Cellular IoT Connectivity Vendor Hub
27/09/2022
What were the travel trends this summer?
21/09/2022
Ubigi: 5G now available in more than 20 countries at no extra cost
16/09/2022
Iphone 14 – Ubigi : Why the end of the physical SIM card is great news for travellers?
12/09/2022
What does traveler data consumption reveal?
29/07/2022
Ubigi launches a mobile Internet rate calculator for travelers abroad
28/07/2022
Transatel launches its global 5G IoT connectivity solution in Japan with NTT DOCOMO
16/06/2022
The benefits of eSIM for British tourism professionals
14/06/2022
Transatel kicks off its global 5G IoT deployment in France.
04/05/2022
Best Practices for Scaling IoT Internationally
20/04/2022
Transatel supports Ukrainian refugees with free Ubigi eSIM connectivity
01/04/2022
Meet Transatel at Channel Live 22
22/03/2022
Transatel launches new Bullitt Group MVNO in the UK for rugged mobile devices.
01/03/2022
Transatel announces private LTE/5G extension solution
25/02/2022
Perenio and Transatel announced cooperation to empower enterprises’ distributed workforce
23/02/2022
EU roaming fees are back in the UK and eSIM data plans could be a cost-effective alternative for travelers
20/01/2022
Transatel participates in the New Symphonie consortium
14/12/2021
German telecom regulator BNetzA sides with Transatel in its regulatory dispute with Telefónica.
03/12/2021
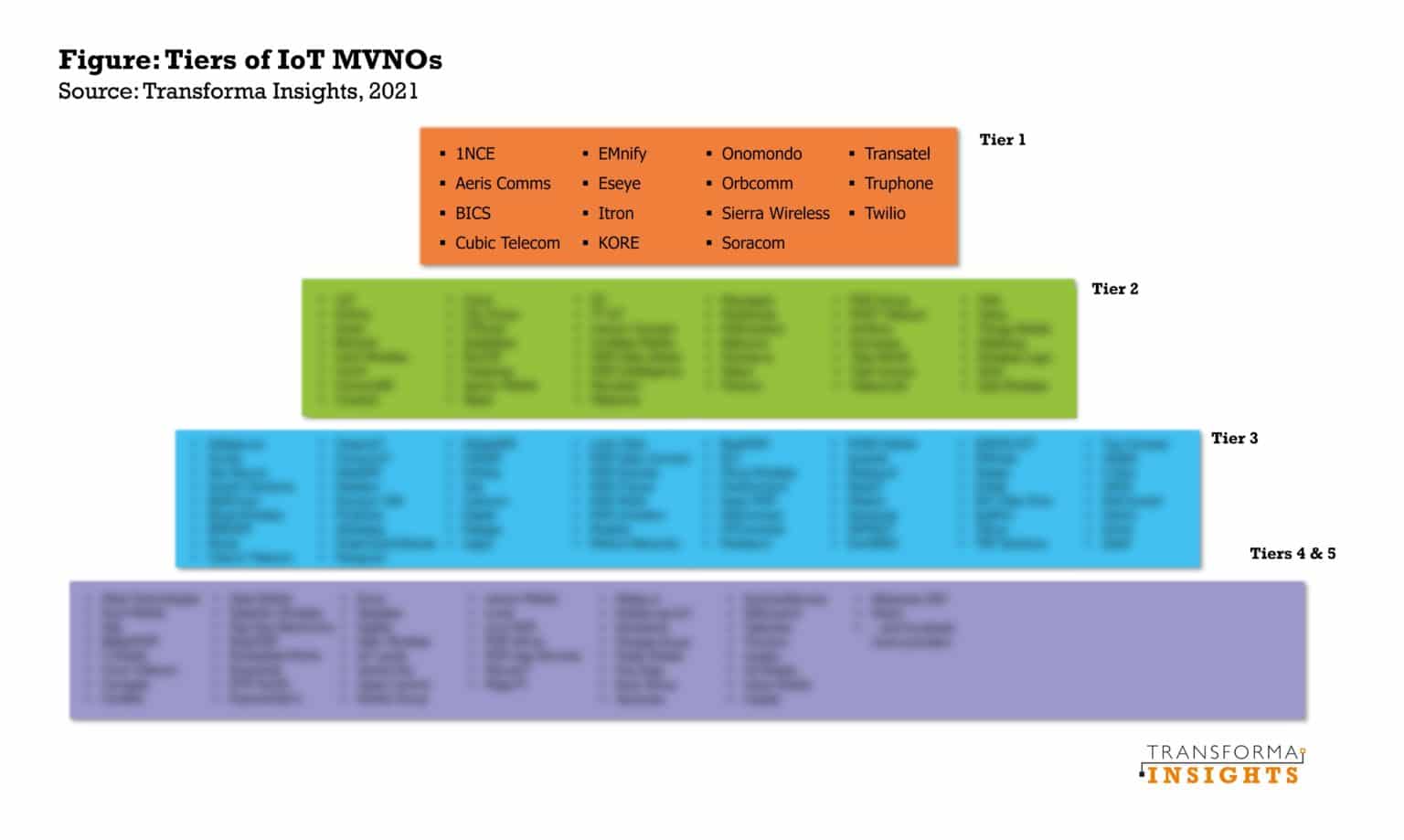
Transatel ranked Tier 1 IoT MVNO by Transforma Insights
19/11/2021
Meet Transatel’s team at the IoT World & M2M on the 5th and 6th of October 2021!
24/09/2021
Where can you meet us? Transatel 2021 events
08/09/2021
Amazon Alexa in-car voice service now available in the Uconnect Services for the New Jeep® Compass
05/05/2021
Meet Transatel at the Mobile World Congress 2021!
28/04/2021
Jacques Bonifay, online panelist at the annual Wireless Russia & CIS 2020 forum
02/11/2020
Transatel is shortlisted for the IoT Global Awards!
28/10/2020
Transatel is now on WeChat. Join us!
21/10/2020
Transatel and Ledger “Most compliant” at IoT Awards 2020!
24/09/2020
Transatel is in the top 3 Best MVNO Partners according to the Mobile Industry Awards 2020!
23/09/2020
We are proud to be shortlisted for the final of the 2020 Mobile Industry Awards as the best MVNO Partner!!!
18/05/2020
We’re at MWC 2020, in Hall 2! Click here to meet us there.
07/02/2020
Transatel is at IoT Solutions World Congress, Barcelona (October 29th – 31st)
15/10/2019
Transatel is at WIK Conference 2019 (October 15 & 16)
02/10/2019
Transatel is at NTT Communications Forum, Tokyo (October 3 – 4) at booth IoT Connect Mobile! Click here to book a meeting
24/09/2019
Transatel is at ITS world congress Singapore (October 21 – 25) at booth #493! Click here to book a meeting
23/09/2019
Transatel is at MVNO Europe/ e-SIM Connect (October 14 & 15) at booth #18! Click here to book a meeting
20/09/2019
Transatel is at TU-Automotive Europe (October 29 & 30) at booth #7! Click here to book a meeting
02/09/2019
Transatel is at Channel Live 2019 (Sep 11 & 12) at booth #631! Click here to know more…
28/08/2019
We’re at MVNOs World Congress Amsterdam (May 21 – 24) at booth 16! Click here to meet us there…
14/05/2019
Transatel is at Utility Week Live (May 21 & 22) at booth H12! Click here to know more…
09/05/2019
We’re at IoT Tech Expo London (April 25 & 26) at booth 500 ! Click here to meet us there…
24/04/2019
Ubimobility 2019 (June 3 – 14), Chicago : Transatel chosen among 8 French tech companies by Business France & BPI France
23/04/2019
We’re at SIDO Lyon (April 10-11)! Click to meet us there…
08/04/2019
Bienvenue à notre meetup sur l’Industrie 4.0, le 28 mars chez Transatel
28/03/2019
We’re at Mobile World Congress 2019 (February 25-28) in Barcelona! Click here to meet us there…
04/02/2019
Transatel will be at Automotive World (January 16-18) in Tokyo! Click to know more
24/12/2018
We’re at CES 2019 (January 8-11) in Las Vegas! Click here to meet us there…
We’re at ecta Regulatory Conference (November 27–28) in Brussels! Click here to meet us there…
30/10/2018
J. Bonifay & R. Durand speaking at MVNO Europe/eSIM Connect, Nov 6.
25/10/2018
We’re at TU-Automotive Munich (October 30 & 31) at booth P4! Click here to meet us there…
We’re at Qualcomm 4G/5G Summit (October 22–24) in Hong Kong! Click to meet us there…
10/10/2018
Transatel rejoint la Fédération Française des Télécoms
03/10/2018
We’re at Mondial Tech (October 2-6) at booth F40! Click here to meet us there…
17/09/2018
We’re at Channel Live Birmingham (September 11-12) at booth 552! Click here to meet us there…
30/07/2018
We’re at the 2018 ConCar Expo (June 27 – 28 ) in Berlin! Click here to meet us there…
21/06/2018
We’re at the Webit Festival (June 25 – 27) in Sofia! Click to meet us there…
18/06/2018
Computex 2018: Transatel to power Gemalto and Qualcomm LTE demos
05/06/2018
We’re recruiting! Our CEO details our opportunities on BFM Business… Replay the excerpt here!
21/05/2018
We’re at the IoT Connected Smart Cars & Vehicles Forum (May 23- 24) in Berlin! Click here to meet us there…
07/05/2018
We’re at the Utility Week Live Birmingham (May 21- 22) at booth D35! Click here to meet us there…
06/05/2018
Transatel wins ‘Best IoT Enabler’ at MVNOs World Congress 2018
03/05/2018
We’re at IoT Tech Expo London (April 25 & 26) at booth 500 ! Click here to meet us there…
04/04/2018
ECTA welcomes Transatel as new member
20/02/2018
We’re at the Connected Driver in Brussels, Feb. 7-8!
07/02/2018
Romain Durand to speak at 2nd World eSIM, Feb. 8-9, Berlin
Transatel Listed Among Prominent Vendors In Connected Car, M2M Connections and Services in SEA Market
17/01/2018
Transatel Technology Presented by Major OEMs at CES 2018, Meet Us There!
09/01/2018
Acer Launches the New Swift 7, Redefining the World’s Thinnest Laptop
06/01/2018
Transatel Listed Among Top Global Players in The Mobile Value Added Market
04/01/2018
Launch of the ASUS Transformer Mini (T103HAF) with native 4G/LTE
11/12/2017
Transatel and China Mobile partner to launch CMLink
10/12/2017
On Nov 29th, J. Bonifay to speak at the annual ECTA Regulatory Conference
16/11/2017
Meet us at stand #46 at the TU Automotive in Munich on Nov. 6th and 7th!
02/11/2017
On Nov 14th, J.Bonifay to speak at MVNO Europe. Meet us on stand #12
01/11/2017
B.Salomon to speak at eSIM Connect 2017 in London, from Nov. 14th!
17/10/2017
On Oct 17th, Jacques Bonifay to speak at MVNOs North America event in Chicago
01/10/2017
Meet us in Barcelona at the IoT Solutions World Congress, October 3-5, 2017
27/09/2017
Meet us in Marrakech at the GSMA WAS#6 , September 26th – 28th, 2017
13/09/2017
On 15 Sep, J. Bonifay takes part in EU’s roundtable on Connected Cars at IAA Frankfurt
04/09/2017
Meet us at the Channel Live in Birmingham on September 12th and 13th!
08/08/2017
Jacques Bonifay is part of the Global Device Summit on June 29th! Book a meeting here.
20/06/2017
Bertrand Salomon to talk at the Connected Cars and Autonomous Vehicles London on June 15th! Arrange a meeting below…
14/06/2017
Jacques Bonifay to speak at IoT Tech Expo Europe in Berlin! Click here to meet with us…
10/05/2017
Meet us at the MVNO World Congress 2017 in Nice from April 24th!
18/04/2017
Meet us in Macau at the GSMA WAS #5 from March 27th!
17/03/2017
We’re at the Mobile World Congress 2017 from Feb. 27th! Room 2C45.
27/01/2017
Jacques Bonifay to speak at the MVNO Networking Congress in London November 2nd! Click here to see us there…
06/10/2016
We’re at meeting space #5 at the WAS in Dublin the 31st of October! Click here to meet us there…
30/08/2016
L’Expansion once again ranks Transatel amongst top independent French companies!
29/08/2016
Jacques Bonifay, speaker at the Aviation Festival 9th of September. Click here to meet us at stand 17!
22/07/2016
We’re at the MWC 2016 in Shanghai July 1st! Click here to meet us there…
22/06/2016
We’re at the MVNO World Congress at stand #42! Click here to meet us there…
11/04/2016
Jacques Bonifay to speak at the MVNO World Congress 2016
10/04/2016
Nous serons présents au WAS #3 à Bruxelles du 7 au 10 mars 2016! Suivez ce lien pour nous rencontrer…
29/02/2016
We’re at the MWC 2016 in Barcelona 22 – 25 Feb! Click here to meet us there…
22/02/2016
We’re at the CES 2016 in Las Vegas Jan. 6 – 9! Click here to meet us there….
08/01/2016
Dec. 7th-15th: French Tech Tour Japan, South Korea & Taiwan. Meet us there!
20/11/2015
Register here to meet us at the MVNOs Industry Summit Nov. 18th & 19th
16/11/2015
Register here to meet us at AfricaCom from Nov. 17th to 19th!
Transatel Official Member of Economic Delegation to Korea – Nov. 4 – 6th, 2015
04/11/2015
B. Salomon Speaker at the MVNO Networking Congress in London, Nov. 2nd – 4th, 2015
Transatel Present at Japan IT Week, Oct. 28 – 30th, 2015. Meet Us There !
27/10/2015
Meet us in Bangkok at the GSMA WAS#2, Oct.19th – 22nd, 2015
08/09/2015
J. Bonifay to speak at the MVNO Networking Congress in London, Nov. 2nd – 4th, 2015
Jacques Bonifay speaker at the BEREC 2015 Stakeholder Forum – October 15th, 2015
17/08/2015
BARG #85 Dubai – 16 – 19 March 2015
14/03/2015
Mobile World Congress 2015 – Barcelona 2 – 5 March 2015
28/02/2015
CES Las Vegas 2015 – January 6-9, 2015
02/01/2015
MVNO Networking Congress 2014
02/11/2014
BARG #84 – October 20-23, 2014
20/10/2014
M2M Innovation World Congress 2014
21/09/2014
Roaming World Congress 2014 – 12 – 14 May 2014
12/05/2014
Telco Cloud World Forum 2014 – 28-30 April
28/04/2014
MVNOs World Congress 2014 – 8-10 April 2014
08/04/2014
Mobile World Congress 2014 – 24th to 27th of February
24/02/2014
European Competition Forum 2014
11/02/2014
Thank you!
Your message has been send to us.
Close